The content of the article:
- 1 Why does this error appear
- 2 How to solve the error in the CredSSP protocol
- 2.1 Installing Updates
- 2.2 Disabling notifications through the local group editor politicians
- 2.2.1 What to do if the OS does not have the “Correction” parameter encryption oracle vulnerabilities?
- 3 How to control the installation of updates in the enterprise
Why does this error appear
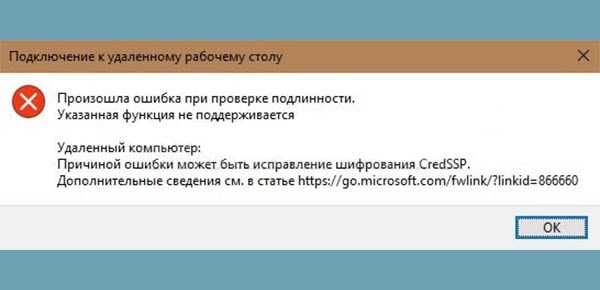
Let’s see in detail why this error occurs. The fact is that March 2018 was marked by the release of Microsoft update that denied connecting to remote desktops (To RDP servers), as Vulnerabilities detected in CredSSP places. And, if on the Windows OS installed on our computer, March updates were not automatically installed, then in May In 2018, RDP connection was completely impossible. Reason this became a complete default ban, due to which users cannot connect to remote desktop from old version of the CredSSP protocol. This appears on the screen message.
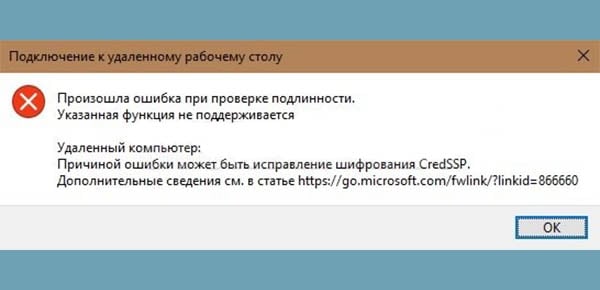
CredSSP Error Message
So what needs to be done to fix this error?
How to solve the error in the CredSSP protocol
Those who have already faced the consequences of introducing relevant Microsoft updates are advised to do the following. Necessary:
- Install the necessary update version from the official site CVE-2018-0886, choosing it for your Windows OS.
- If you cannot patch the CredSSP protocol, then simply disable encryption error notifications.
The second method is not recommended because problem “cause of error maybe CredSSP encryption fix doesn’t resolve, but maybe help temporarily not receive error notifications and therefore gaining popularity among users.
The first thing to do is enable manual mode in the installation updates. Then, whatever you do, to temporarily turn off error notifications, updates still need to be installed, otherwise it fails to connect to the remote desktop.
Install Updates
Each version of Windows has its own update, which You need to install from the Microsoft Central Organ catalog. Below we find the right version CVE-2018-0886 for its operating system:
KB4103721 – Windows 10 1803, Server 2016 1803. KB4103727 – Windows 10 1709, Server 2016 1709. KB4103731 – Windows 10 1703, Server 2016 1703. KB4103723 – Windows 10 1607, Server 2016 1607, Server 2016. KB4103728 – Windows 10 1511, Server 2016 1511. KB4103716 – Windows 10. KB4103715 – Windows 8.1, Server 2012 R2, Server 2012. KB4103712 – Windows 7, Server 2008 R2.
Click on the name of your OS and download the desired patch.
Turn off notifications through the local group editor politicians
Open the local group policy editor by typing in The Run line of the gpedit.msc command. Before us is such window.
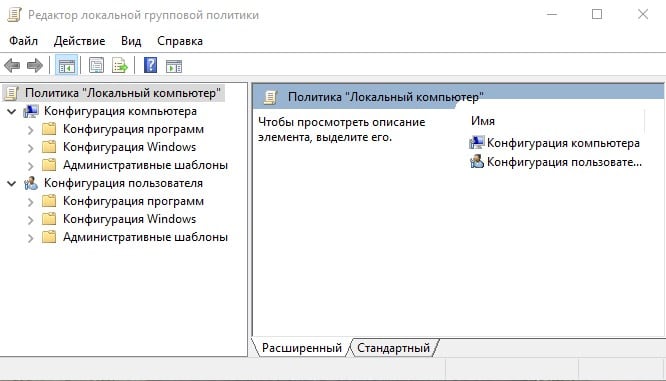
Local Group Policy Editor Window
- Далее проходим путь “Конфигурация компьютера” –>“Административные шаблоны” –> “Система” –> “Передача учетныхdata ”.
- We are looking for the option “Fix encryption oracle vulnerability” and We translate it into the state “ON”.
- We set the “Leave vulnerability” protection level.
- That’s it, we reboot the device and try to connect to remote desktop.
What to do if the OS does not have the option “Vulnerability Fix” encryption oracle “?
- In this case, we register the necessary parameters in the registry manually.
- In the line “Run” we type the regedit command.
- In the registry editor that opens, go along the path HKLM \ Software \ Microsoft \ Windows \ CurrentVersion \ Policies \ System \ CredSSP \ Parameters.
- Here we are looking for a DWORD parameter called AllowEncryptionOracle and assign it a value of 2.
- If this parameter is not in our Windows, then create it.
- Be sure to restart the device and continue to work.
You can go the other way:
- Open command prompt as administrator.
- Enter REG ADD HKLM \ SOFTWARE \ Microsoft \ Windows \ CurrentVersion \ Policies \ System \ CredSSP \ Parameters / v AllowEncryptionOracle / t REG_DWORD / d 2.
- Confirm action.
- Put the computer on a reboot.
Using this command, we make changes to the registry, which Allows our device to connect using the CredSSP protocol.
How to control the installation of updates in the enterprise
In order to install current updates immediately on all local devices of the enterprise, the server must have WSUS program. With its help, control over the installed updates, the correct installation of which is reflected in the received reports.
Whatever the way to bypass connection blocking to Remote Desktop, this measure is temporary. For uninterrupted the work of the enterprise must constantly monitor the release of updates and install them on time.